What Are RFID Cards?
RFID cards are access cards embedded with RFID chips that store and transmit data when in proximity to RFID readers. These cards are commonly used in access control systems to grant or restrict entry to specific areas based on the permissions assigned to the cardholder.
Typically, RFID cards function by utilizing radio frequency signals to communicate with RFID readers. When a card is presented to a reader, the reader detects the unique ID stored on the card's chip and verifies it against the access control system's database to determine whether access should be granted or denied.
RFID cards come in various forms, including key cards, badges, and smart cards, each offering different levels of security and functionality. These cards play a crucial role in modern access control systems, providing convenience and enhanced security for organizations of all sizes.
What is an RFID access control system?
An RFID access control system is a security solution that uses RFID technology to manage and control access to buildings, rooms, or specific areas within a facility. This system consists of RFID readers, RFID cards or key fobs, and access control software that work together to secure premises and monitor entry and exit activities.
With an RFID access control system, administrators can easily assign access permissions to individuals or groups, track movements within the premises, and generate detailed access logs for security purposes. This system offers a more efficient and secure alternative to traditional lock-and-key mechanisms.
By leveraging RFID technology, access control systems can enhance overall security, streamline operations, and provide a seamless experience for authorized personnel while keeping unauthorized individuals at bay.
How does an RFID access control system work?
An RFID access control system works by using RFID technology to authenticate and authorize individuals' entry into secure areas. When a person presents an RFID card or key fob to an RFID reader, the reader scans the card's information and sends it to the access control software for verification.
The access control software compares the card's data against the predefined access permissions stored in the system. If the information matches and the individual has the necessary authorization, the door or barrier is unlocked, granting access. If there is a mismatch or lack of authorization, access is denied, and an alert may be triggered to notify security personnel.
RFID access control systems provide a convenient and secure way to manage access to restricted areas, improve operational efficiency, and bolster overall security measures within an organization.
Advantages of RFID Card Access Control Systems
-
Enhanced Security and Convenience: RFID Card Access Control Systems enable contactless entry, reducing physical wear and increasing the speed of access. The wireless technology ensures a smoother and more efficient user experience.
-
Flexible and Scalable Administration: Administrators can effortlessly manage user access, adding or revoking rights remotely without needing physical changes to the system. This flexibility supports organizational growth and changes without significant overhead.
-
Detailed Audit Trails: The systems provide comprehensive logs of user access, including entry times and locations. This is crucial for security audits, incident investigations, and enforcing access policies.
-
Integrated Security Solutions: RFID systems can be seamlessly integrated with other security measures such as surveillance cameras and alarm systems. This holistic approach enhances overall security and monitoring capabilities.
-
Reduced Duplication Risk: The unique encryption and identification features of RFID cards make them more secure against duplication compared to traditional keys. This significantly lowers the risk of unauthorized access.
Types of access control systems
Key Fob Door Entry systems
Key fob door entry systems are a popular type of access control solution that utilizes RFID technology to grant access to authorized individuals. These systems typically consist of key fobs embedded with RFID chips and corresponding readers installed at entry points.
When a user presents their key fob to the reader, the system verifies the fob's information against the access control database and grants access if the permissions are met. Key fob door entry systems are commonly used in residential buildings, offices, and gated communities for secure entry.
While key fob door entry systems offer convenience and security, it's essential to ensure proper encryption and security measures are in place to prevent unauthorized access or manipulation of the system.
How Does Key Card Access Control Work?
Key card access control systems operate similarly to RFID card systems, with individuals using key cards embedded with RFID chips to gain access to controlled areas. When a user presents their key card to an RFID reader, the reader scans the card's data and verifies it against the access control system's database.
If the cardholder has the necessary permissions, the access control system unlocks the door or barrier, allowing entry. Key card access control systems offer increased security and convenience compared to traditional key-based systems, as lost or stolen cards can be easily deactivated and replaced.
Organizations can customize key card access control systems to suit their specific security needs, such as implementing multi-factor authentication or integrating with other security systems for enhanced protection.
Badge access systems
Badge access systems utilize badges embedded with RFID technology to grant individuals entry to secured areas. These badges are often personalized with the user's name, photo, and other identifying information, making them ideal for use in organizations with high-security requirements.
When a badge is presented to an RFID reader, the system verifies the user's identity and access permissions before allowing entry. Badge access systems are commonly used in government facilities, corporate offices, and healthcare institutions where strict access control measures are essential.
Organizations can leverage badge access systems to enhance security, monitor access activities, and restrict entry to sensitive areas based on individual roles and responsibilities within the organization.
Proximity card lock systems
Proximity card lock systems are a type of access control solution that utilizes proximity cards to grant or deny access to designated areas. These cards do not require physical contact with the reader; instead, they function within close proximity, making access control more convenient and user-friendly.
When a proximity card is brought near an RFID reader, the reader detects the card's signal and verifies the user's access permissions in real-time. Proximity card lock systems are commonly used in hotels, educational institutions, and commercial buildings for hassle-free access management and enhanced security.
Organizations can benefit from proximity card lock systems by implementing additional security features, such as biometric verification, to further strengthen access control measures and prevent unauthorized entry.
Magnetic card door access reader systems
Magnetic card door access reader systems utilize magnetic stripe cards to grant access to authorized individuals. These cards contain a magnetic stripe that stores user information, which is read by a magnetic card reader connected to an access control system.
When a magnetic card is swiped through the reader, the system verifies the card's data against the access permissions set in the system's database. If the information matches and the user has the necessary authorization, access is granted, allowing entry into the secured area.
Magnetic card door access reader systems offer a cost-effective and secure access control solution for organizations looking to restrict entry to specific areas without the need for complex technology or infrastructure. However, it's essential to ensure proper encryption and secure data storage to prevent unauthorized access or data breaches.
Key Components of RFID Access Control Security Systems
RFID Tags (Transponders):
RFID tags are small electronic devices embedded with a chip and an antenna, designed to receive and respond to radio-frequency queries from an RFID reader. They can be passive, active, or battery-assisted passive, with varying ranges and capabilities. Passive tags are powered by the reader's signal, whereas active tags have their own power source, allowing for longer range and larger memory capacities. These tags store the identification and other information about the item or person they are attached to.
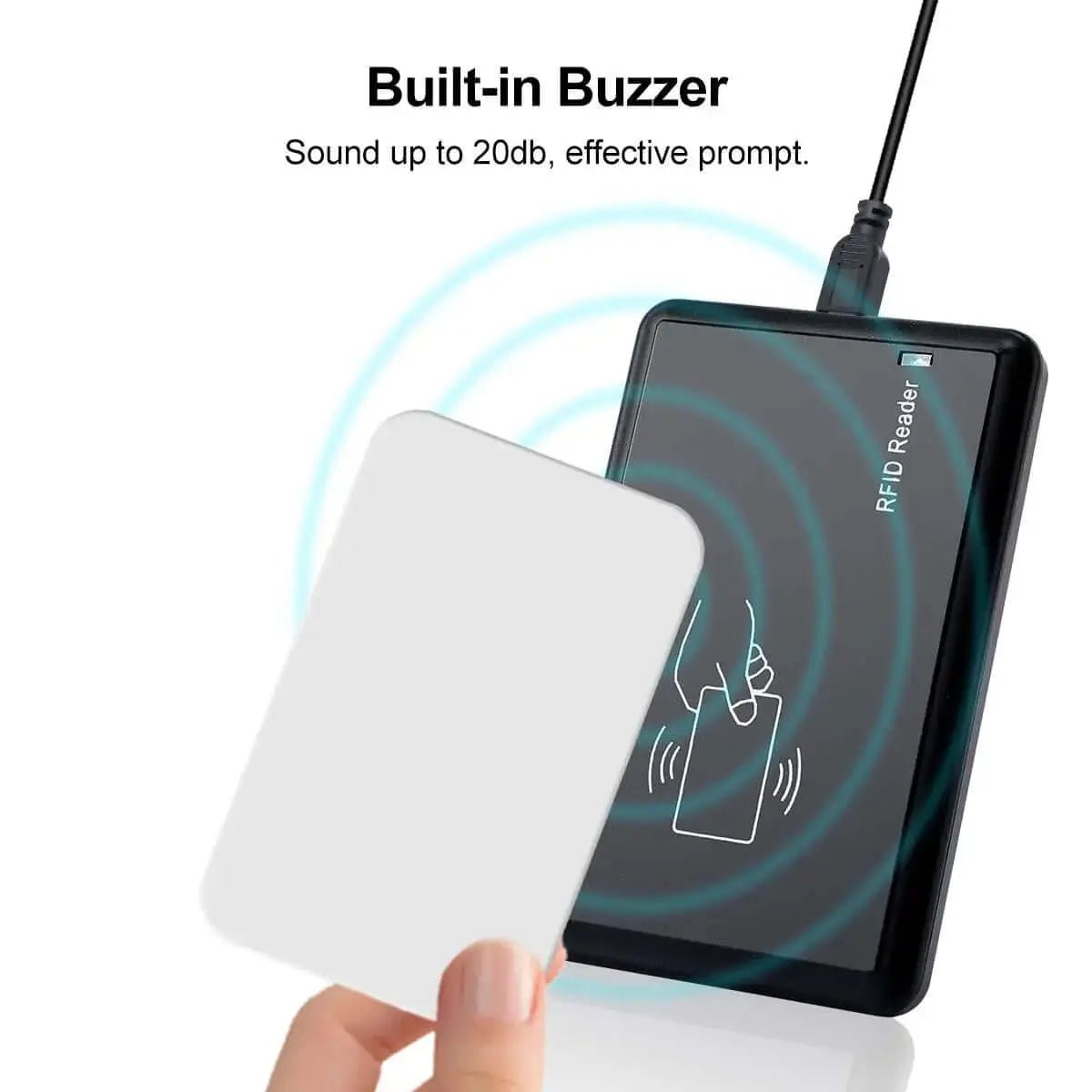
RFID Readers (Interrogators):
RFID readers are devices that send out radio waves to detect and communicate with RFID tags. They can read the information stored on an RFID tag and pass it to a processing system. Readers vary in range, frequency, and configuration (handheld, stationary, etc.). They are critical for the access control system, as they are the point of contact between the system and the tag-bearing individuals or items.
Access Control Server (ACS):
The Access Control Server is the central hub of the RFID security system, responsible for processing the data received from RFID readers and making access control decisions. It maintains a database of authorized RFID tag IDs and their corresponding user or item information. The ACS can trigger alarms, open gates, or deny access based on the comparison of the tag data against the access control lists.
Antennas:
Antennas are crucial for the transmission and reception of radio waves between the RFID reader and RFID tags. They come in various shapes and sizes, tailored to specific operational frequencies and environments. The antenna's design affects the system's range and efficiency. They can be built into the reader or installed separately, depending on the system's requirements.
Network Infrastructure:
The network infrastructure connects RFID readers, access control servers, and other system components, facilitating communication and data transfer between them. This can include wired connections (like Ethernet) or wireless technologies (such as Wi-Fi or cellular). It's crucial for real-time data processing and for integrating the RFID system with other security and monitoring systems.
Software and User Interface:
The software component of an RFID access control system is responsible for data analysis, user management, and system configuration. It provides a user interface for administrators to set rules, add or remove tags from the system, monitor access events, and generate reports. The software can also integrate with other security systems, offering a comprehensive security solution.
Encryption and Security Protocols:
To prevent unauthorized access and ensure data integrity, RFID systems use encryption and secure communication protocols. This includes encrypting the data stored on tags and the data transmitted between tags and readers. Security protocols also protect against eavesdropping, data tampering, and cloning, ensuring that only authorized devices and individuals can access and communicate within the system.
Physical Security Measures:
In addition to electronic components, physical security measures are crucial to protect RFID equipment and the areas they secure. This includes locks, barriers, tamper-evident seals, and secure installations of readers and antennas. These measures prevent physical tampering and ensure the reliability of the RFID system as part of a broader security strategy.
Active vs. passive RFID access control systems:
- Active RFID systems rely on battery-powered tags that actively transmit signals to RFID readers, offering longer read ranges and real-time tracking capabilities.
- Passive RFID systems, on the other hand, use electromagnetic signals from readers to power up and transmit data, making them more cost-effective for access control applications.
You can read a detailed explanation of difference between Active and Passive RFID here.
Security Features to Look For in an RFID Door Access System:
When selecting an RFID door access system, it's essential to consider security features such as:
Encryption Protocols
Look for systems using AES (Advanced Encryption Standard) or other secure, contemporary encryption methods to safeguard the transmission of data.
Ensure end-to-end encryption where not just the tag-reader communication is encrypted, but also the data transmission between the reader and the access control server.
Multi-Factor Authentication (MFA) Options
MFA adds layers of security by requiring more than one form of verification before granting access. This can significantly reduce the risk of unauthorized access due to lost or cloned RFID tags.
Consider systems that require a combination of something the user has (an RFID card), something the user knows (a PIN or password), and something the user is (biometric verification like fingerprint or facial recognition).
Flexible MFA settings allow for adjustable security levels depending on the sensitivity of the area being protected.
Tamper Detection Mechanisms
Tamper detection ensures that any attempt to physically compromise the reader or the control panel triggers an alert, contributing to the system's physical security integrity.
Opt for devices that have active monitoring for tampering, such as removing the device from the wall or attempting to open the casing.
Integrated alarm systems or notifications can alert security personnel in real time if tampering is detected
Audit Trail Capabilities
Audit trails record every instance of access or attempted access, providing a historical data trail that can be critical for security audits, investigations, and compliance.
Ensure the system can log and store detailed access events including successful and unsuccessful access attempts, time of access, and user identification.
Look for systems with easy-to-use reporting tools that allow for quick analysis and review of access logs for any given timeframe.
Additional Considerations
- Compliance and Standards: Depending on your region and industry, ensure the system complies with relevant standards and regulations.
- Scalability: The system should be able to grow with your needs without significant overhauls.
- User Management: Efficiently add, remove, or modify user access levels as needed.
- Integration capabilities: The ability to integrate with other security systems such as video surveillance or alarm systems can enhance overall security posture.
These security features help prevent unauthorized access, mitigate security risks, and ensure the integrity of the access control system.
Choose the Right Access Control Card Reader Type for Your Business
Choosing the right access control card reader is a critical decision for ensuring the security and efficiency of an organization. Here's a detailed breakdown of the factors you mentioned that should be considered to make an informed choice:
Read Range
- Short-range readers are suitable for single-person access points where space is limited, or close proximity verification is desired for added security.
- Long-range readers are better for vehicle access or any situation where the cardholder cannot easily reach the reader. Consider the environment and purpose of the reader to decide which read range is most practical and secure.
Compatibility with Existing Systems:
Check if the new card readers can integrate seamlessly with your organization's existing access control system, security cameras, and alarm systems. This can save costs and reduce complications during installation.
Consider the communication standards and protocols (like Wiegand, OSDP, etc.) supported by both the existing system and the new readers to ensure they can communicate efficiently.
Ease of Integration:
The card reader technology should be user-friendly and not require extensive training for administrators and users. User interfaces should be intuitive, and the system software should allow for easy addition or removal of access permissions.
Look for readers with streamlined installation processes and strong technical support from the manufacturer or vendor. This will lessen downtime and reduce installation costs.
Future Scalability:
Consider how easy it will be to expand your access control system in the future. Can the system support more readers and a larger number of users as your organization grows?
Ensure the technology is adaptable and can be updated to meet future security challenges. For example, choose readers that support firmware updates for new features or security patches.
By selecting the right access control card reader, you can enhance security, streamline access management processes, and improve overall operational efficiency within your organization.